CIRCL/vulnerability-severity-classification-roberta-base
Text Classification • 0.1B • Updated
• 1.37k • • 8
id stringlengths 12 47 | title stringlengths 0 256 ⌀ | description stringlengths 3 189k | cpes listlengths 0 5.42k | cvss_v4_0 float64 0 10 ⌀ | cvss_v3_1 float64 0 10 ⌀ | cvss_v3_0 float64 0 10 ⌀ | cvss_v2_0 float64 0 10 ⌀ | patch_commit_url stringlengths 36 232 ⌀ |
|---|---|---|---|---|---|---|---|---|
GHSA-jj67-w8gj-6whm | In validateIconUserBoundary of PrintManagerService.java, there is a possible cross-user image leak due to a confused deputy. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation. | [] | null | 7.8 | null | null | null | |
GHSA-jhq5-xcpf-vrwm | A vulnerability in the Cisco SD-WAN Solution could allow an unauthenticated, remote attacker to bypass certificate validation on an affected device. The vulnerability is due to improper certificate validation. An attacker could exploit this vulnerability by supplying a system image signed with a crafted certificate to an affected device, bypassing the certificate validation. An exploit could allow an attacker to deploy a crafted system image. | [] | null | 9.8 | null | null | null | |
GHSA-v27w-q35g-5rp9 | CMS Made Simple 2.2.10 has XSS via the myaccount.php "Email Address" field, which is reachable via the "My Preferences -> My Account" section. | [] | null | null | 5.4 | null | null | |
CVE-2017-11853 | Windows kernel in Windows 7 SP1, Windows Server 2008 SP2 and R2 SP1, Windows 8.1 and RT 8.1, Server 2012 and R2, Windows 10 Gold, 1511, 1607, 1703, and 1709, Windows Server 2016, and Windows Server, version 1709 allows an attacker to log in and run a specially crafted application due to the Windows kernel improperly initializing a memory address, aka "Windows Kernel Information Disclosure Vulnerability". This CVE ID is unique from CVE-2017-11842, CVE-2017-11849, and CVE-2017-11851. | [
"cpe:2.3:o:microsoft:windows_10:*:*:*:*:*:*:*:*",
"cpe:2.3:o:microsoft:windows_10:1511:*:*:*:*:*:*:*",
"cpe:2.3:o:microsoft:windows_10:1607:*:*:*:*:*:*:*",
"cpe:2.3:o:microsoft:windows_10:1703:*:*:*:*:*:*:*",
"cpe:2.3:o:microsoft:windows_10:1709:*:*:*:*:*:*:*",
"cpe:2.3:o:microsoft:windows_7:*:sp1:*:*:*:*... | null | null | 5.5 | 4.3 | null | |
GHSA-9h84-qmv7-982p | Helm Charts with Specific JSON Schema Values Can Cause Memory Exhaustion | A Helm contributor discovered that it was possible to craft a JSON Schema file in a manner which could cause Helm to use all available memory and have an out of memory (OOM) termination.ImpactA malicious chart can point `$ref` in _values.schema.json_ to a device (e.g. `/dev/*`) or other problem file which could cause Helm to use all available memory and have an out of memory (OOM) termination.PatchesThis issue has been resolved in Helm v3.18.5.WorkaroundsMake sure that all Helm charts that are being loaded into Helm doesn't have any reference of `$ref` pointing to `/dev/zero`.ReferencesHelm's security policy is spelled out in detail in our [SECURITY](https://github.com/helm/community/blob/master/SECURITY.md) document.CreditsDisclosed by Jakub Ciolek at AlphaSense. | [] | null | 6.5 | null | null | null |
CVE-2013-5423 | IBM Flex System Manager (FSM) 1.1 through 1.3 before 1.3.2.0 allows remote attackers to enumerate user accounts via unspecified vectors. | [
"cpe:2.3:a:ibm:flex_system_manager:1.1.0:*:*:*:*:*:*:*",
"cpe:2.3:a:ibm:flex_system_manager:1.2.0:*:*:*:*:*:*:*",
"cpe:2.3:a:ibm:flex_system_manager:1.2.1:*:*:*:*:*:*:*",
"cpe:2.3:a:ibm:flex_system_manager:1.3.0:*:*:*:*:*:*:*",
"cpe:2.3:a:ibm:flex_system_manager:1.3.1:*:*:*:*:*:*:*"
] | null | null | null | 5 | null | |
GHSA-q2wf-pr3p-9rhr | A vulnerability has been found in CodeAstro Online Railway Reservation System 1.0 and classified as problematic. Affected by this vulnerability is an unknown functionality of the file /admin/admin-update-employee.php of the component Update Employee Page. The manipulation of the argument emp_fname /emp_lname /emp_nat_idno/emp_addr leads to cross site scripting. The attack can be launched remotely. The exploit has been disclosed to the public and may be used. | [] | 5.1 | 2.4 | null | null | null | |
CVE-2013-6497 | clamscan in ClamAV before 0.98.5, when using -a option, allows remote attackers to cause a denial of service (crash) as demonstrated by the jwplayer.js file. | [
"cpe:2.3:a:clamav:clamav:*:*:*:*:*:*:*:*"
] | null | null | null | 2.1 | null | |
CVE-2025-4304 | PHPGurukul Cyber Cafe Management System adminprofile.php sql injection | A vulnerability, which was classified as critical, was found in PHPGurukul Cyber Cafe Management System 1.0. This affects an unknown part of the file /adminprofile.php. The manipulation of the argument mobilenumber leads to sql injection. It is possible to initiate the attack remotely. The exploit has been disclosed to the public and may be used. Other parameters might be affected as well. | [] | 6.9 | 7.3 | 7.3 | 7.5 | null |
GHSA-6w5f-5wgr-qjg5 | Constellation allows Emergency shell access during initramfs boot phase | ImpactAn active attacker could let the boot fail on purpose in the initramfs, dropping the serial console into an emergency shell. This gives attackers with access to the serial console full control over the VM.PatchesThe issue has been patched in [v2.6.0](https://github.com/edgelesssys/constellation/releases/tag/v2.6.0).Workaroundsnone | [] | null | null | null | null | null |
GHSA-gwcq-g2m6-5993 | ChakraCore and Microsoft Edge in Microsoft Windows 10 Gold, 1511, 1607, 1703, and Windows Server 2016 allows an attacker to execute arbitrary code in the context of the current user, due to how the scripting engine handles objects in memory, aka "Scripting Engine Memory Corruption Vulnerability". This CVE ID is unique from CVE-2017-11792, CVE-2017-11793, CVE-2017-11796, CVE-2017-11797, CVE-2017-11798, CVE-2017-11799, CVE-2017-11800, CVE-2017-11801, CVE-2017-11802, CVE-2017-11804, CVE-2017-11805, CVE-2017-11806, CVE-2017-11807, CVE-2017-11808, CVE-2017-11809, CVE-2017-11810, CVE-2017-11812, and CVE-2017-11821. | [] | null | null | 7.5 | null | null | |
GHSA-h3q5-gjcc-wrm3 | The WPQA Builder WordPress plugin before 6.1.1 does not have CSRF checks in some places, which could allow attackers to make logged in users perform unwanted actions via CSRF attacks | [] | null | 8.8 | null | null | null | |
GHSA-ggp3-c9px-5c4p | If Thunderbird was configured to use STARTTLS for an IMAP connection, and an attacker injected IMAP server responses prior to the completion of the STARTTLS handshake, then Thunderbird didn't ignore the injected data. This could have resulted in Thunderbird showing incorrect information, for example the attacker could have tricked Thunderbird to show folders that didn't exist on the IMAP server. This vulnerability affects Thunderbird < 78.12. | [] | null | 5.9 | null | null | null | |
GHSA-wjrx-6529-hcj3 | HashiCorp go-getter Vulnerable to Symlink Attacks | HashiCorp's go-getter library subdirectory download feature is vulnerable to symlink attacks leading to unauthorized read access beyond the designated directory boundaries. This vulnerability, identified as CVE-2025-8959, is fixed in go-getter 1.7.9. | [] | null | 7.5 | null | null | null |
GHSA-fx4h-f9f2-xm3r | WebKit, as used in Apple iTunes before 10.7, allows remote attackers to execute arbitrary code or cause a denial of service (memory corruption and application crash) via a crafted web site, a different vulnerability than other WebKit CVEs listed in APPLE-SA-2012-09-12-1. | [] | null | null | null | null | null | |
CVE-2007-6573 | QK SMTP Server 3 allows remote attackers to cause a denial of service (daemon crash) via a long (1) HELO, (2) MAIL FROM, or (3) RCPT TO command; or (4) a long string in the message sent after the DATA command; possibly a related issue to CVE-2006-5551. | [
"cpe:2.3:a:qksoft:qk_smtp_server_3:*:*:*:*:*:*:*:*"
] | null | null | null | 7.8 | null | |
GHSA-gf4w-r33x-hg8c | Telerik Fiddler through 5.0.20202.18177 allows attackers to execute arbitrary programs via a hostname with a trailing space character, followed by --utility-and-browser --utility-cmd-prefix= and the pathname of a locally installed program. The victim must interactively choose the Open On Browser option. Fixed in version 5.0.20204. | [] | null | 8.8 | null | null | null | |
GHSA-pg6q-9mqp-879x | Blesta 3.x through 5.x before 5.13.3 allows object injection, aka CORE-5668. | [] | null | 7.2 | null | null | null | |
CVE-2018-14584 | An issue has been discovered in Bento4 1.5.1-624. AP4_AvccAtom::Create in Core/Ap4AvccAtom.cpp has a heap-based buffer over-read. | [
"cpe:2.3:a:axiosys:bento4:1.5.1-624:*:*:*:*:*:*:*"
] | null | null | 8.8 | 6.8 | null | |
GHSA-p6j5-5ppm-w335 | Cisco IOS 12.1T, 12.2, 12.2T, 12.3 and 12.3T, with Multi Protocol Label Switching (MPLS) installed but disabled, allows remote attackers to cause a denial of service (device reload) via a crafted packet sent to the disabled interface. | [] | null | null | null | null | null | |
GHSA-9wf4-422v-6w3j | An arbitrary file upload vulnerability in the importSettings method of VisiCut v2.1 allows attackers to execute arbitrary code via uploading a crafted Zip file. | [] | null | 9.8 | null | null | null | |
CVE-2017-18026 | Redmine before 3.2.9, 3.3.x before 3.3.6, and 3.4.x before 3.4.4 does not block the --config and --debugger flags to the Mercurial hg program, which allows remote attackers to execute arbitrary commands (through the Mercurial adapter) via vectors involving a branch whose name begins with a --config= or --debugger= substring, a related issue to CVE-2017-17536. | [
"cpe:2.3:a:redmine:redmine:*:*:*:*:*:*:*:*",
"cpe:2.3:o:debian:debian_linux:9.0:*:*:*:*:*:*:*"
] | null | null | 8.8 | 6.8 | null | |
GHSA-8mwm-rmq7-g8j8 | The Debug Log Manager plugin for WordPress is vulnerable to Cross-Site Request Forgery in all versions up to, and including, 2.2.1. This is due to missing or incorrect nonce validation on the clear_log() function. This makes it possible for unauthenticated attackers to clear the debug log via a forged request granted they can trick a site administrator into performing an action such as clicking on a link. | [] | null | 4.3 | null | null | null | |
ICSA-21-287-01 | Schneider Electric CNM | The affected product has an issue with privilege management, which could cause an arbitrary command execution when the software is configured with specially crafted event actions.CVE-2021-22801 has been assigned to this vulnerability. A CVSS v3 base score of 7.8 has been calculated; the CVSS vector string is (AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H). | [] | null | null | 7.8 | null | null |
CVE-2022-22741 | When resizing a popup while requesting fullscreen access, the popup would have become unable to leave fullscreen mode. This vulnerability affects Firefox ESR < 91.5, Firefox < 96, and Thunderbird < 91.5. | [
"cpe:2.3:a:mozilla:firefox:*:*:*:*:*:*:*:*",
"cpe:2.3:a:mozilla:firefox_esr:*:*:*:*:*:*:*:*",
"cpe:2.3:a:mozilla:thunderbird:*:*:*:*:*:*:*:*"
] | null | 7.5 | null | null | null | |
CVE-2005-0446 | Squid 2.5.STABLE8 and earlier allows remote attackers to cause a denial of service (crash) via certain DNS responses regarding (1) Fully Qualified Domain Names (FQDN) in fqdncache.c or (2) IP addresses in ipcache.c, which trigger an assertion failure. | [
"cpe:2.3:a:squid:squid:2.0.patch1:*:*:*:*:*:*:*",
"cpe:2.3:a:squid:squid:2.0.patch2:*:*:*:*:*:*:*",
"cpe:2.3:a:squid:squid:2.0.pre1:*:*:*:*:*:*:*",
"cpe:2.3:a:squid:squid:2.0.release:*:*:*:*:*:*:*",
"cpe:2.3:a:squid:squid:2.0_patch2:*:*:*:*:*:*:*",
"cpe:2.3:a:squid:squid:2.1.patch1:*:*:*:*:*:*:*",
"cpe:... | null | null | null | 5 | null | |
GHSA-wf33-6x33-wcf9 | rdiffweb vulnerable to Authentication Bypass by Primary Weakness | In rdiffweb prior to 2.5.5, the username field is not unique to users. This allows exploitation of primary key logic by creating the same name with different combinations & may allow unauthorized access. | [] | 8.6 | 7.2 | null | null | null |
CVE-2000-0446 | Buffer overflow in MDBMS database server allows remote attackers to execute arbitrary commands via a long string. | [
"cpe:2.3:a:marty_bochane:mdbms:0.9_xbx:*:*:*:*:*:*:*"
] | null | null | null | 7.5 | null | |
GHSA-pjrm-r843-cm53 | : Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting') vulnerability in itemlookup.asp of Telos Automated Message Handling System allows a remote attacker to inject arbitrary script into an AMHS session. This issue affects: Telos Automated Message Handling System versions prior to 4.1.5.5. | [] | null | null | null | null | null | |
CVE-2014-8658 | Cross-site scripting (XSS) vulnerability in RefinedWiki Original Theme 3.x before 3.5.13 and 4.x before 4.0.12 for Confluence allows remote authenticated users with permissions to create or edit content to inject arbitrary web script or HTML via the versionComment parameter to pages/doeditpage.action. | [
"cpe:2.3:a:refinedwiki:refinedwiki_original_theme:3.5:*:*:*:*:confluence:*:*",
"cpe:2.3:a:refinedwiki:refinedwiki_original_theme:3.5.1:*:*:*:*:confluence:*:*",
"cpe:2.3:a:refinedwiki:refinedwiki_original_theme:3.5.2:*:*:*:*:confluence:*:*",
"cpe:2.3:a:refinedwiki:refinedwiki_original_theme:3.5.3:*:*:*:*:confl... | null | null | null | 4 | null | |
GHSA-f7vc-4ggw-hjjh | In Omron CX-Supervisor Versions 3.30 and prior, parsing malformed project files may cause a stack-based buffer overflow. | [] | null | 5.3 | null | null | null | |
CVE-2020-25084 | QEMU 5.0.0 has a use-after-free in hw/usb/hcd-xhci.c because the usb_packet_map return value is not checked. | [
"cpe:2.3:a:qemu:qemu:5.0.0:-:*:*:*:*:*:*",
"cpe:2.3:o:debian:debian_linux:9.0:*:*:*:*:*:*:*",
"cpe:2.3:o:debian:debian_linux:10.0:*:*:*:*:*:*:*"
] | null | 3.2 | null | 2.1 | null | |
CVE-2022-27172 | A hard-coded password vulnerability exists in the console infactory functionality of InHand Networks InRouter302 V3.5.37. A specially-crafted network request can lead to privileged operation execution. An attacker can send a sequence of requests to trigger this vulnerability. | [
"cpe:2.3:o:inhandnetworks:ir302_firmware:*:*:*:*:*:*:*:*",
"cpe:2.3:h:inhandnetworks:ir302:-:*:*:*:*:*:*:*"
] | null | null | 4.3 | null | null | |
GHSA-xxv5-m8w5-gxh4 | Jensen of Scandinavia Eagle 1200AC V15.03.06.33_en was discovered to contain a stack overflow via the wrlEn_5g parameter at /goform/WifiBasicSet. | [] | null | 6.5 | null | null | null | |
GHSA-6pg5-wf6r-xvh8 | In the Linux kernel, the following vulnerability has been resolved:arcnet: Add NULL check in com20020pci_probe()devm_kasprintf() returns NULL when memory allocation fails. Currently,
com20020pci_probe() does not check for this case, which results in a
NULL pointer dereference.Add NULL check after devm_kasprintf() to prevent this issue and ensure
no resources are left allocated. | [] | null | 5.5 | null | null | null | |
CVE-2024-25986 | In ppmp_unprotect_buf of drm_fw.c, there is a possible compromise of protected memory due to a logic error in the code. This could lead to local escalation of privilege to TEE with no additional execution privileges needed. User interaction is not needed for exploitation. | [
"cpe:2.3:o:google:android:*:*:*:*:*:*:*:*"
] | null | 7.8 | null | null | null | |
GHSA-gf4j-rqc4-f9q2 | Cross-site scripting (XSS) vulnerability in uddiclient/process in the UDDI client in SAP NetWeaver Application Server (Java) 7.0 allows remote attackers to inject arbitrary web script or HTML via the TModel Key field. | [] | null | null | null | null | null | |
GHSA-2j7f-m85p-rvqj | The UserLogin control in BEA WebLogic Portal 8.1 through Service Pack 3 prints the password to standard output when an incorrect login attempt is made, which could make it easier for attackers to guess the correct password. | [] | null | null | null | null | null | |
RHSA-2024:8111 | Red Hat Security Advisory: skopeo security update | encoding/gob: golang: Calling Decoder.Decode on a message which contains deeply nested structures can cause a panic due to stack exhaustion | [
"cpe:/a:redhat:enterprise_linux:9::appstream"
] | null | 7.5 | null | null | null |
CVE-2020-7054 | MmsValue_decodeMmsData in mms/iso_mms/server/mms_access_result.c in libIEC61850 through 1.4.0 has a heap-based buffer overflow when parsing the MMS_BIT_STRING data type. | [
"cpe:2.3:a:mz-automation:libiec61850:*:*:*:*:*:*:*:*"
] | null | 8.8 | null | 6.8 | null | |
GHSA-qhqp-w648-gwgc | Windows Clustered Shared Volume Information Disclosure Vulnerability. This CVE ID is unique from CVE-2022-29120, CVE-2022-29122, CVE-2022-29123. | [] | null | 6.5 | null | null | null | |
GHSA-2c5c-cr43-hgwm | SQL injection vulnerability in saa.php in Andy's PHP Knowledgebase (Aphpkb) 0.95.3 and earlier allows remote attackers to execute arbitrary SQL commands via the aid parameter, a different vulnerability than CVE-2011-1546. NOTE: some of these details are obtained from third party information. | [] | null | null | null | null | null | |
GHSA-8vm8-w94h-5m67 | Subrion CMS 4.0.5 has CSRF in admin/blog/add/. The attacker can add any tag, and can optionally insert XSS via the tags parameter. | [] | null | null | 8.8 | null | null | |
CVE-2007-5052 | Multiple cross-site scripting (XSS) vulnerabilities in index.php in Vigile CMS 1.8 allow remote attackers to inject arbitrary web script or HTML via a request to the wiki module with (1) the title parameter or (2) a "title=" sequence in the PATH_INFO, or a request to the download module with (3) the cat parameter or (4) a "cat=" sequence in the PATH_INFO. | [
"cpe:2.3:a:itcms:vigile_cms:1.8:*:*:*:*:*:*:*"
] | null | null | null | 4.3 | null | |
GHSA-6rvp-82jr-vcfr | Inappropriate implementation in Media in Google Chrome prior to 141.0.7390.54 allowed a remote attacker who convinced a user to engage in specific UI gestures to perform UI spoofing via a crafted HTML page. (Chromium security severity: Medium) | [] | null | 6.3 | null | null | null | |
GHSA-949p-32jv-ghmg | The raw_cmd_copyout function in drivers/block/floppy.c in the Linux kernel through 3.14.3 does not properly restrict access to certain pointers during processing of an FDRAWCMD ioctl call, which allows local users to obtain sensitive information from kernel heap memory by leveraging write access to a /dev/fd device. | [] | null | null | null | null | null | |
GHSA-7h2p-gcjg-4fw8 | In the Linux kernel, the following vulnerability has been resolved:scsi: lpfc: Fix null pointer dereference in lpfc_prep_els_iocb()It is possible to call lpfc_issue_els_plogi() passing a did for which no
matching ndlp is found. A call is then made to lpfc_prep_els_iocb() with a
null pointer to a lpfc_nodelist structure resulting in a null pointer
dereference.Fix by returning an error status if no valid ndlp is found. Fix up comments
regarding ndlp reference counting. | [] | null | 5.5 | null | null | null | |
GHSA-2x4x-73fj-7gr8 | NVIDIA Tegra Gralloc module contains a vulnerability in driver in which it does not validate input parameter of the registerbuffer API, which may lead to arbitrary code execution, denial of service, or escalation of privileges. Android ID: A-62540032 Severity Rating: High Version: N/A. | [] | null | null | 7.8 | null | null | |
GHSA-mqgr-4p27-366c | A vulnerability, which was classified as critical, has been found in SourceCodester Vehicle Service Management System 1.0. Affected by this issue is some unknown functionality of the file view_service.php. The manipulation of the argument id leads to sql injection. The attack may be launched remotely. The exploit has been disclosed to the public and may be used. The identifier of this vulnerability is VDB-226100. | [] | null | 9.8 | null | null | null | |
CVE-2008-0625 | Buffer overflow in the MediaGrid ActiveX control (mediagrid.dll) in Yahoo! Music Jukebox 2.2.2.56 allows remote attackers to execute arbitrary code via a long argument to the AddBitmap method. | [
"cpe:2.3:a:yahoo:music_jukebox:2.2.2.56:*:*:*:*:*:*:*"
] | null | null | null | 4.3 | null | |
CVE-2025-11299 | Belkin F9K1015 formWanTcpipSetup buffer overflow | A vulnerability was identified in Belkin F9K1015 1.00.10. The affected element is an unknown function of the file /goform/formWanTcpipSetup. The manipulation of the argument pppUserName leads to buffer overflow. It is possible to initiate the attack remotely. The exploit is publicly available and might be used. The vendor was contacted early about this disclosure but did not respond in any way. | [
"cpe:2.3:o:belkin:f9k1015_firmware:*:*:*:*:*:*:*:*"
] | 8.7 | 8.8 | 8.8 | 9 | null |
GHSA-fgxx-cm7r-ghp7 | The Anviz Management System for access control has insufficient logging for device events such as door open requests. | [] | null | null | null | null | null | |
GHSA-r4w3-3p9j-2qrw | Stack-based buffer overflow in the Helper class in the yt.ythelper.2 ActiveX control in Yahoo! Toolbar 1.4.1 allows remote attackers to cause a denial of service (browser crash) via a long argument to the c method. | [] | null | null | null | null | null | |
CVE-2006-4135 | PHP remote file inclusion vulnerability in cal_config.inc.php in Calendarix 0.7.20060401 and earlier allows remote attackers to execute arbitrary PHP code via a URL in the calpath parameter. NOTE: this issue has been disputed by a third party, who says that the affected $calpath variable is set to a constant value in the beginning of the script. CVE concurs that the initial report is invalid | [
"cpe:2.3:a:vincent_hor:calendarix:*:*:*:*:*:*:*:*"
] | null | null | null | 7.5 | null | |
GHSA-rf2j-mp54-f2jq | In ih264d_fmt_conv_420sp_to_420p of ih264d_utils.c, there is an out of bound write due to a missing out of bounds check because of a multiplication error. This could lead to an remote code execution with no additional execution privileges needed. User interaction is needed for exploitation. Product: Android. Versions: 6.0, 6.0.1, 7.0, 7.1.1, 7.1.2, 8.0, 8.1. Android ID: A-71375536. | [] | null | null | 7.8 | null | null | |
CVE-2014-3528 | Apache Subversion 1.0.0 through 1.7.x before 1.7.17 and 1.8.x before 1.8.10 uses an MD5 hash of the URL and authentication realm to store cached credentials, which makes it easier for remote servers to obtain the credentials via a crafted authentication realm. | [
"cpe:2.3:o:opensuse:opensuse:12.3:*:*:*:*:*:*:*",
"cpe:2.3:o:opensuse:opensuse:13.1:*:*:*:*:*:*:*",
"cpe:2.3:a:apache:subversion:1.0.0:*:*:*:*:*:*:*",
"cpe:2.3:a:apache:subversion:1.0.1:*:*:*:*:*:*:*",
"cpe:2.3:a:apache:subversion:1.0.2:*:*:*:*:*:*:*",
"cpe:2.3:a:apache:subversion:1.0.3:*:*:*:*:*:*:*",
... | null | null | null | 4 | null | |
GHSA-f5g7-95g9-j55q | An access control issue in Zammad v5.0.3 broadcasts administrative configuration changes to all users who have an active application instance, including settings that should only be visible to authenticated users. | [] | null | 4.3 | null | null | null | |
GHSA-36qh-3xp5-xv7p | A later variation on the Teardrop IP denial of service attack, a.k.a. Teardrop-2. | [] | null | null | null | null | null | |
CVE-2017-14269 | EE 4GEE WiFi MBB (before EE60_00_05.00_31) devices allow remote attackers to obtain sensitive information via a JSONP endpoint, as demonstrated by passwords and SMS content. | [
"cpe:2.3:o:ee:4gee_wifi_mbb_firmware:*:*:*:*:*:*:*:*",
"cpe:2.3:h:ee:4gee_wifi_mbb:-:*:*:*:*:*:*:*"
] | null | null | 9.8 | 5 | null | |
cisco-sa-sna-prvesc-4BQmK33Z | Cisco Secure Network Analytics Privilege Escalation Vulnerability | A vulnerability in the web-based management interface of Cisco Secure Network Analytics could allow an authenticated, remote attacker with valid administrative credentials to execute arbitrary commands as root on the underlying operating system.
This vulnerability is due to insufficient integrity checks within device backup files. An attacker with valid administrative credentials could exploit this vulnerability by crafting a malicious backup file and restoring it to an affected device. A successful exploit could allow the attacker to obtain shell access on the underlying operating system with the privileges of root.
Cisco has released software updates that address this vulnerability. There are no workarounds that address this vulnerability.
| [] | null | 6 | null | null | null |
GHSA-2h79-f8wh-7h2v | All versions of Dingtian DT-R002 are vulnerable to an Insufficiently Protected Credentials vulnerability that could allow an attacker to extract the proprietary "Dingtian Binary" protocol password by sending an unauthenticated GET request. | [] | 8.7 | 7.5 | null | null | null | |
GHSA-67gp-34xw-p93j | Google Chrome before 7.0.517.44 does not properly handle the data types of event objects, which allows remote attackers to cause a denial of service or possibly have unspecified other impact via unknown vectors. | [] | null | 9.8 | null | null | null | |
GHSA-g265-w27f-7cfm | Use of entitlement "com.apple.security.cs.disable-library-validation" and lack of launch and library load constraints allows to substitute a legitimate dylib with malicious one. A local attacker with unprivileged access can execute the application with altered dynamic library successfully bypassing Transparency, Consent, and Control (TCC). Acquired resource access is limited to previously granted permissions by the user. Access to other resources beyond granted-permissions requires user interaction with a system prompt asking for permission.This issue affects DaVinci Resolve on macOS in all versions.
Last tested version: 19.1.3 | [] | 4.8 | null | null | null | null | |
GHSA-438m-xg9x-7hw2 | C/sorting/binary_insertion_sort.c in The Algorithms - C through e5dad3f has a segmentation fault for deep recursion, which may affect common use cases such as sorting an array of 50 elements. | [] | null | 6.2 | null | null | null | |
CVE-2021-36159 | libfetch before 2021-07-26, as used in apk-tools, xbps, and other products, mishandles numeric strings for the FTP and HTTP protocols. The FTP passive mode implementation allows an out-of-bounds read because strtol is used to parse the relevant numbers into address bytes. It does not check if the line ends prematurely. If it does, the for-loop condition checks for the '\0' terminator one byte too late. | [
"cpe:2.3:a:freebsd:libfetch:*:*:*:*:*:*:*:*"
] | null | 9.1 | null | 6.4 | null | |
GHSA-g237-5cc4-cmqg | BattleBlog stores sensitive information under the web root with insufficient access control, which allows remote attackers to download a database via a direct request for database/blankmaster.mdb. | [] | null | null | null | null | null | |
CVE-2006-3180 | Cross-site scripting (XSS) vulnerability in ftp_index.php in Confixx Pro 3.0 allows remote attackers to inject arbitrary web script or HTML via the path parameter. | [
"cpe:2.3:a:swsoft:confixx:pro_3:*:*:*:*:*:*:*"
] | null | null | null | 6.8 | null | |
CVE-2017-10888 | BOOK WALKER for Windows Ver.1.2.9 and earlier, BOOK WALKER for Mac Ver.1.2.5 and earlier allow an attacker to access local files via unspecified vectors. | [
"cpe:2.3:a:bookwalker:book_walker:*:*:*:*:*:*:*:*",
"cpe:2.3:o:microsoft:windows:-:*:*:*:*:*:*:*",
"cpe:2.3:o:apple:macos:-:*:*:*:*:*:*:*"
] | null | null | 5.5 | 4.3 | null | |
GHSA-hf79-3hfm-mgmr | The radio frequency communication protocol being used by Meross MSH30Q 4.5.23 is vulnerable to replay attacks, allowing attackers to record and replay previously captured communication to execute unauthorized commands or actions (e.g., thermostat's temperature). | [] | null | 8.8 | null | null | null | |
GHSA-fjx4-mcpx-mwq6 | The (1) fw_cfg_write and (2) fw_cfg_read functions in hw/nvram/fw_cfg.c in QEMU before 2.4, when built with the Firmware Configuration device emulation support, allow guest OS users with the CAP_SYS_RAWIO privilege to cause a denial of service (out-of-bounds read or write access and process crash) or possibly execute arbitrary code via an invalid current entry value in a firmware configuration. | [] | null | null | 8.1 | null | null | |
GHSA-86gj-qj6h-cwmx | KeePassXC-Browser thru 1.9.9.2 autofills or prompts to fill stored credentials into documents rendered under a browser-enforced CSP directive and iframe attribute sandbox, allowing attacker-controlled script in the sandboxed document to access populated form fields and exfiltrate credentials. | [] | null | 7.1 | null | null | null | |
CVE-2018-4254 | In macOS High Sierra before 10.13.5, an input validation issue existed in the kernel. This issue was addressed with improved input validation. | [
"cpe:2.3:o:apple:mac_os_x:*:*:*:*:*:*:*:*"
] | null | null | 9.8 | 10 | null | |
GHSA-q52j-4q2q-hcj6 | Authentication Bypass in console-io | Affected versions of the `console-io` package do not configure the underlying websocket library to require authentication, resulting in an authentication bypass vulnerability. As `console-io` allows terminal access on the server via a web page, an authentication bypass is essentially remote code execution.RecommendationUpdate to version 2.3.0 or later. | [] | null | null | 9.8 | null | null |
CVE-2023-2523 | Weaver E-Office unrestricted upload | A vulnerability was found in Weaver E-Office 9.5. It has been rated as critical. Affected by this issue is some unknown functionality of the file App/Ajax/ajax.php?action=mobile_upload_save. The manipulation of the argument upload_quwan leads to unrestricted upload. The attack may be launched remotely. The exploit has been disclosed to the public and may be used. VDB-228014 is the identifier assigned to this vulnerability. NOTE: The vendor was contacted early about this disclosure but did not respond in any way. | [
"cpe:2.3:a:e-office:e-office:9.5:*:*:*:*:*:*:*"
] | null | 7.3 | 7.3 | 7.5 | null |
CVE-2022-33879 | Incomplete fix and new regex DoS in StandardsExtractingContentHandler | The initial fixes in CVE-2022-30126 and CVE-2022-30973 for regexes in the StandardsExtractingContentHandler were insufficient, and we found a separate, new regex DoS in a different regex in the StandardsExtractingContentHandler. These are now fixed in 1.28.4 and 2.4.1. | [
"cpe:2.3:a:apache:tika:*:*:*:*:*:*:*:*"
] | null | 3.3 | null | 2.6 | null |
GHSA-5rg2-8583-83hq | Missing Authorization vulnerability in merkulove Gmaper for Elementor allows Exploiting Incorrectly Configured Access Control Security Levels.This issue affects Gmaper for Elementor: from n/a through 1.0.9. | [] | null | 5.4 | null | null | null | |
CVE-2020-0652 | A remote code execution vulnerability exists in Microsoft Office software when the software fails to properly handle objects in memory, aka 'Microsoft Office Memory Corruption Vulnerability'. | [
"cpe:2.3:a:microsoft:excel:2010:sp2:*:*:*:*:*:*",
"cpe:2.3:a:microsoft:excel:2013:sp1:*:*:*:*:*:*",
"cpe:2.3:a:microsoft:excel:2013:sp1:*:*:rt:*:*:*",
"cpe:2.3:a:microsoft:excel:2016:*:*:*:*:*:*:*",
"cpe:2.3:a:microsoft:excel:2019:*:*:*:*:*:*:*",
"cpe:2.3:a:microsoft:office_365_proplus:-:*:*:*:*:*:*:*"
] | null | 7.8 | null | 6.8 | null | |
GHSA-4xq8-m4f5-h82h | In the Linux kernel, the following vulnerability has been resolved:usb: fix various gadgets null ptr deref on 10gbps cabling.This avoids a null pointer dereference in
f_{ecm,eem,hid,loopback,printer,rndis,serial,sourcesink,subset,tcm}
by simply reusing the 5gbps config for 10gbps. | [] | null | 5.5 | null | null | null | |
CVE-2025-53656 | Jenkins ReadyAPI Functional Testing Plugin 1.11 and earlier stores SLM License Access Keys, client secrets, and passwords unencrypted in job config.xml files on the Jenkins controller, where they can be viewed by users with Item/Extended Read permission or access to the Jenkins controller file system. | [] | null | 6.5 | null | null | null | |
CVE-2017-11557 | An issue was discovered in ZOHO ManageEngine Applications Manager 12.3. It is possible for an unauthenticated user to view the list of domain names and usernames used in a company's network environment via a userconfiguration.do?method=editUser request. | [
"cpe:2.3:a:zohocorp:manageengine_applications_manager:12.3:*:*:*:*:*:*:*"
] | null | null | 5.3 | 5 | null | |
GHSA-32v2-jqqh-g63h | Vulnerabilities exist in the BIOS implementation of Aruba 9200 and 9000 Series Controllers and Gateways that could allow an attacker to execute arbitrary code early in the boot sequence. An attacker could exploit this vulnerability to gain access to and change underlying sensitive information in the affected controller leading to complete system compromise. | [] | null | 8 | null | null | null | |
RHSA-2019:2746 | Red Hat Security Advisory: rh-nginx112-nginx security update | HTTP/2: large amount of data requests leads to denial of service HTTP/2: flood using PRIORITY frames results in excessive resource consumption HTTP/2: 0-length headers lead to denial of service | [
"cpe:/a:redhat:rhel_software_collections:3::el7"
] | null | null | 6.5 | null | null |
GHSA-h42x-xx2q-6v6g | Flowise Pre-auth Arbitrary File Upload | SummaryAn unauthorized attacker can leverage the whitelisted route `/api/v1/attachments` to upload arbitrary files when the `storageType` is set to **local** (default).DetailsWhen a new request arrives, the system first checks if the URL starts with `/api/v1/`. If it does, the system then verifies whether the URL is included in the whitelist (*whitelistURLs*). If the URL is whitelisted, the request proceeds; otherwise, the system enforces authentication.@ */packages/server/src/index.ts***The whitelist is defined as follows**This means that every route in the whitelist does not require authentication. Now, let's examine the `/api/v1/attachments` route.@ */packages/server/src/routes/attachments/index.ts*After several calls, the request reaches the `createFileAttachment` function @ (*packages/server/src/utils/createAttachment.ts*)
Initially, the function retrieves *chatflowid* and *chatId* from the request without any additional validation. The only check performed is whether these parameters exist in the request.Next, the function retrieves the uploaded files and attempts to add them to the storage by calling the `addArrayFilesToStorage` function.Now lets take a look at `addArrayFilesToStorage` function @ (*/packages/components/src/storageUtils.ts*)As noted in the comment, to construct the directory, the function joins the output of the `getStoragePath` function with `...paths`, which are essentially the `chatflowid` and `chatId` extracted earlier from the request.
However, as mentioned previously, these values are not validated to ensure they are UUIDs or numbers. As a result, an attacker could manipulate these variables to set the **dir** variable to any value.
Combined with the fact that the filename is also provided by the user, this leads to **unauthenticated arbitrary file upload**.POCThis is the a HTTP request. As observed, we are not authenticated, and by manipulating the `chatId` parameter, we can perform a path traversal. In this example, we overwrite the `api.json` file, which contains the API keys for the system.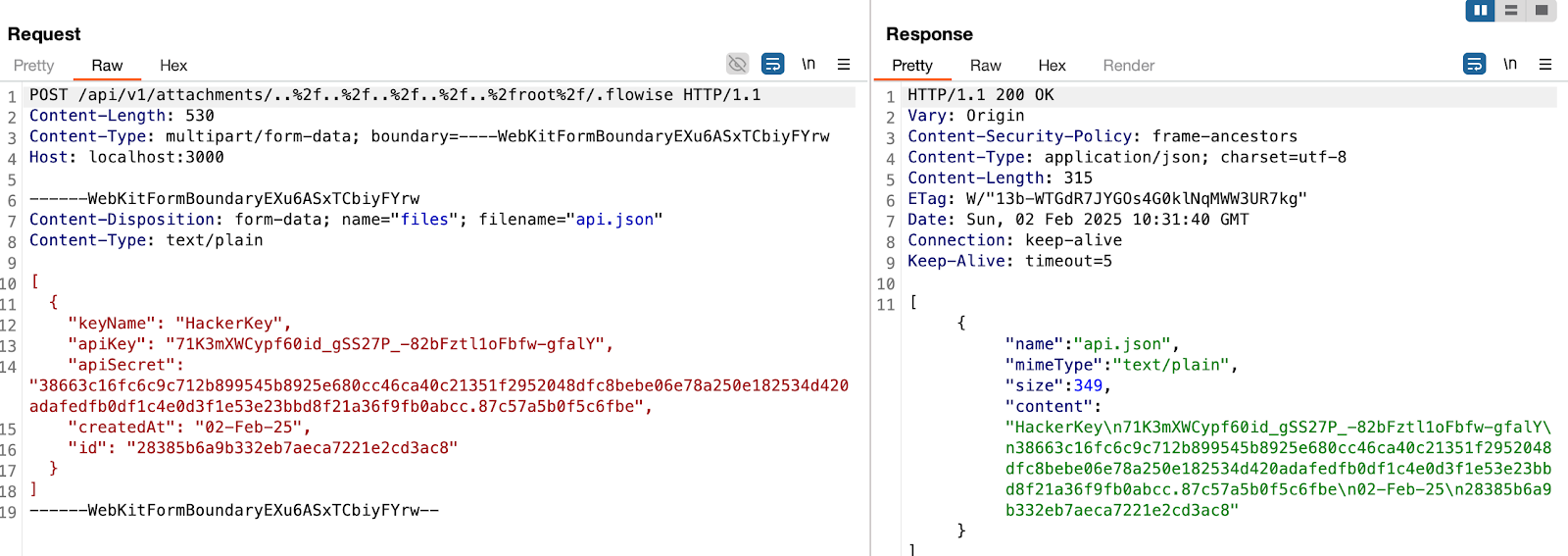in this example, the **dir** variable will beand the file name is `api.json`And the API Keys in the UI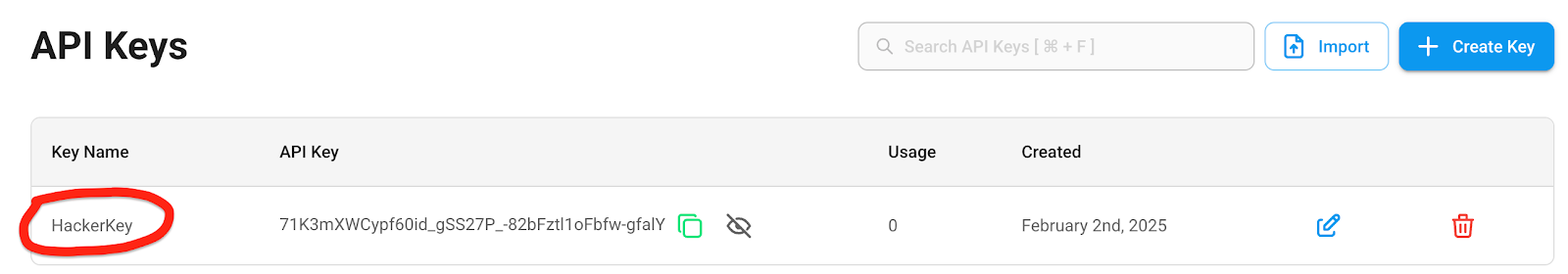ImpactThis vulnerability could potentially lead toRemote Code ExecutionServer TakeoverData Theft
And more | [] | 9.3 | null | null | null | null |
CVE-2017-9041 | GNU Binutils 2.28 allows remote attackers to cause a denial of service (heap-based buffer over-read and application crash) via a crafted ELF file, related to MIPS GOT mishandling in the process_mips_specific function in readelf.c. | [
"cpe:2.3:a:gnu:binutils:2.28:*:*:*:*:*:*:*"
] | null | null | 5.5 | 4.3 | null | |
GHSA-5x2r-hc65-25f9 | ML-DSA Signature Verification Accepts Signatures with Repeated Hint Indices | **Affected Crate:** `ml-dsa`
**Affected Versions:** v0.1.0-rc.2 (and commits since `b01c3b7`)
**Severity:** Medium
**Reporter:** Oren Yomtov (Fireblocks)SummaryThe ML-DSA signature verification implementation in the RustCrypto `ml-dsa` crate incorrectly accepts signatures with repeated (duplicate) hint indices. According to the ML-DSA specification (FIPS 204 / RFC 9881), hint indices within each polynomial must be **strictly increasing**. The current implementation uses a non-strict monotonic check (`<=` instead of `<`), allowing duplicate indices.**Note:** This is a regression bug. The original implementation was correct, but commit `b01c3b7` ("Make ML-DSA signature decoding follow the spec (#895)", fixing issue #894) inadvertently changed the strict `<` comparison to `<=`, introducing the vulnerability.Vulnerability DetailsRoot CauseThe vulnerability is located in the `monotonic` helper function in `ml-dsa/src/hint.rs`:The comparison operator `<=` allows equal consecutive values, meaning duplicate hint indices are not rejected. The correct implementation should use strict less-than (`<`):Regression Analysis**Original correct code** (commit `1d3a1d1` - "Add support for ML-DSA (#877)"): Used `<` (strict)**Bug introduced** (commit `b01c3b7` - "Make ML-DSA signature decoding follow the spec (#895)"): Changed to `<=`The commit message suggests it was intended to fix issue #894 and make decoding follow the spec, but the change to the `monotonic` function was in the wrong direction. The other changes in that commit (to `use_hint` function) may have been correct, but this specific change introduced signature malleability.Technical ImpactThis vulnerability allows **signature malleability** - the same logical signature can have multiple valid byte-level encodings. An attacker can take a valid signature and create additional "valid" signatures by duplicating hint indices.Per the ML-DSA specification (FIPS 204, Section 6.2 and Algorithm 26 `HintBitUnpack`), hint indices must be strictly increasing to ensure a unique, canonical encoding. Accepting non-canonical signatures can lead to:**Signature Malleability:** Multiple distinct byte sequences verify as valid for the same message/key pair**Protocol-Level Vulnerabilities:** Systems that rely on signature uniqueness (e.g., for transaction deduplication, replay protection, or signature-based identifiers) may be vulnerable**Interoperability Issues:** Non-compliant signatures may be rejected by other conforming implementationsAffected Security LevelsAll ML-DSA parameter sets are affected:ML-DSA-44 (NIST Security Level 2)ML-DSA-65 (NIST Security Level 3)ML-DSA-87 (NIST Security Level 5)Proof of ConceptSee the file [`poc_mldsa_repeated_hint.rs`](https://gist.github.com/orenyomtov/fb4616eb77d33017f41a71b30aa41a04) for a standalone proof of concept that demonstrates the vulnerability.The PoC uses test vectors from the Wycheproof test suite that specifically test for this invalid encoding:**Test Vector Source:** [Wycheproof ML-DSA Test Vectors](https://github.com/C2SP/wycheproof/blob/master/testvectors_v1/mldsa_44_verify_test.json)Test Case ID 18: "signature with a repeated hint"Expected Result: `invalid`Actual Result: `valid` (BUG)RemediationUpdate the `monotonic` function in `ml-dsa/src/hint.rs` to use strict less-than comparison:Design Intent: ML-DSA is NOT Intended to Allow MalleabilityWhile some cryptographic libraries intentionally permit signature malleability for compatibility or performance reasons, **ML-DSA is explicitly designed to prevent it**:**FIPS 204 Specification:** ML-DSA is designed to be strongly unforgeable under chosen message attacks (SUF-CMA). This security property explicitly prevents signature malleability.**NIST PQC Forum Discussion:** In February 2024, there was a discussion on the NIST PQC forum about potential malleability in ML-DSA's hint unpacking. The consensus was that ML-DSA is intended to be SUF-CMA, meaning any malleability issues should be considered bugs and fixed.**No Documentation of Intentional Malleability:** There is no documentation in the RustCrypto `ml-dsa` crate, FIPS 204, or RFC 9881 suggesting that signature malleability is an acceptable or intentional property.**Regression Bug:** The fact that the original implementation had strict ordering (`<`) and this was changed to non-strict (`<=`) in a "fix" commit suggests this was an unintentional regression, not a design decision. | [] | null | 5.3 | null | null | null |
CVE-2021-41113 | Cross-Site-Request-Forgery in Backend URI Handling in Typo3 | TYPO3 is an open source PHP based web content management system released under the GNU GPL. It has been discovered that the new TYPO3 v11 feature that allows users to create and share deep links in the backend user interface is vulnerable to cross-site-request-forgery. The impact is the same as described in TYPO3-CORE-SA-2020-006 (CVE-2020-11069). However, it is not limited to the same site context and does not require the attacker to be authenticated. In a worst case scenario, the attacker could create a new admin user account to compromise the system. To successfully carry out an attack, an attacker must trick his victim to access a compromised system. The victim must have an active session in the TYPO3 backend at that time. The following Same-Site cookie settings in $GLOBALS[TYPO3_CONF_VARS][BE][cookieSameSite] are required for an attack to be successful: SameSite=strict: malicious evil.example.org invoking TYPO3 application at good.example.org and SameSite=lax or none: malicious evil.com invoking TYPO3 application at example.org. Update your instance to TYPO3 version 11.5.0 which addresses the problem described. | [
"cpe:2.3:a:typo3:typo3:*:*:*:*:*:*:*:*"
] | null | 8.8 | null | null | null |
CVE-2008-5818 | Directory traversal vulnerability in index.php in eDreamers eDContainer 2.22, when magic_quotes_gpc is disabled, allows remote attackers to include and execute arbitrary local files via a .. (dot dot) in the lg parameter. NOTE: some of these details are obtained from third party information. | [
"cpe:2.3:a:edreamers:edcontainer:2.22:*:*:*:*:*:*:*"
] | null | null | null | 6.8 | null | |
GHSA-4q82-9j8m-c42w | devolo dLAN Cockpit 4.3.1 contains an unquoted service path vulnerability in the 'DevoloNetworkService' that allows local non-privileged users to potentially execute arbitrary code. Attackers can exploit the insecure service path configuration by inserting malicious code in the system root path to execute with elevated privileges during application startup or system reboot. | [] | 8.5 | 8.4 | null | null | null | |
CVE-2018-0799 | Microsoft Access in Microsoft SharePoint Enterprise Server 2013 and Microsoft SharePoint Enterprise Server 2016 allows a cross-site-scripting (XSS) vulnerability due to the way image field values are handled, aka "Microsoft Access Tampering Vulnerability". | [
"cpe:2.3:a:microsoft:sharepoint_enterprise_server:2013:sp1:*:*:*:*:*:*",
"cpe:2.3:a:microsoft:sharepoint_enterprise_server:2016:*:*:*:*:*:*:*"
] | null | null | 6.1 | 4.3 | null | |
GHSA-6mmq-wfvf-jxf6 | A vulnerability allows unauthorized access to functionality inadequately constrained by ACLs. Attackers may exploit this to unauthenticated execute commands potentially leading to unauthorized data manipulation, access to privileged functions, or even the execution of arbitrary code. | [] | null | 10 | null | null | null | |
CVE-2025-1020 | Memory safety bugs present in Firefox 134 and Thunderbird 134. Some of these bugs showed evidence of memory corruption and we presume that with enough effort some of these could have been exploited to run arbitrary code. This vulnerability affects Firefox < 135 and Thunderbird < 135. | [] | null | 9.8 | null | null | null | |
CVE-2014-1564 | Mozilla Firefox before 32.0, Firefox ESR 31.x before 31.1, and Thunderbird 31.x before 31.1 do not properly initialize memory for GIF rendering, which allows remote attackers to obtain sensitive information from process memory via crafted web script that interacts with a CANVAS element associated with a malformed GIF image. | [
"cpe:2.3:o:opensuse:evergreen:11.4:*:*:*:*:*:*:*",
"cpe:2.3:o:opensuse:opensuse:12.3:*:*:*:*:*:*:*",
"cpe:2.3:o:opensuse:opensuse:13.1:*:*:*:*:*:*:*",
"cpe:2.3:a:mozilla:firefox:*:*:*:*:*:*:*:*",
"cpe:2.3:a:mozilla:firefox:30.0:*:*:*:*:*:*:*",
"cpe:2.3:a:mozilla:firefox:31.0:*:*:*:*:*:*:*",
"cpe:2.3:a:m... | null | null | null | 4.3 | null | |
CVE-2024-55542 | Local privilege escalation due to excessive permissions assigned to Tray Monitor service. The following products are affected: Acronis Cyber Protect 16 (Linux, macOS, Windows) before build 39169, Acronis Cyber Protect Cloud Agent (Linux, macOS, Windows) before build 35895. | [] | null | null | 4.4 | null | null | |
GHSA-9v3f-9r8j-jvcj | modules.php in PHP-Nuke 6.x to 7.6 allows remote attackers to obtain sensitive information via a direct request to (1) my_headlines, (2) userinfo, or (3) search, which reveals the path in a PHP error message. | [] | null | null | null | null | null | |
CVE-2024-5741 | XSS in inventory view | Stored XSS in inventory tree rendering in Checkmk before 2.3.0p7, 2.2.0p28, 2.1.0p45 and 2.0.0 (EOL) | [
"cpe:2.3:a:checkmk:checkmk:*:*:*:*:*:*:*:*",
"cpe:2.3:a:checkmk:checkmk:2.1.0:-:*:*:*:*:*:*",
"cpe:2.3:a:checkmk:checkmk:2.1.0:b1:*:*:*:*:*:*",
"cpe:2.3:a:checkmk:checkmk:2.1.0:b2:*:*:*:*:*:*",
"cpe:2.3:a:checkmk:checkmk:2.1.0:b3:*:*:*:*:*:*",
"cpe:2.3:a:checkmk:checkmk:2.1.0:b4:*:*:*:*:*:*",
"cpe:2.3:a... | null | 6.5 | null | null | null |
GHSA-hc24-m26q-hrrw | A vulnerability was found in SourceCodester Task Progress Tracker 1.0 and classified as problematic. Affected by this issue is some unknown functionality of the file update-task.php. The manipulation of the argument task_name leads to cross site scripting. The attack may be launched remotely. The exploit has been disclosed to the public and may be used. | [] | 5.3 | 3.5 | null | null | null | |
GHSA-xf7f-8qhq-f75q | The Advanced Ads – Ad Manager & AdSense plugin for WordPress is vulnerable to Stored Cross-Site Scripting via the Advanced Ad widget in all versions up to, and including, 1.52.1 due to insufficient input sanitization and output escaping on user supplied attributes. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page. | [] | null | 6.4 | null | null | null | |
GHSA-vr74-q73p-p5rh | A vulnerability was found in Tenda A301 15.13.08.12. It has been classified as critical. Affected is the function fromSetWirelessRepeat of the file /goform/WifiExtraSet. The manipulation of the argument wpapsk_crypto leads to stack-based buffer overflow. It is possible to launch the attack remotely. The exploit has been disclosed to the public and may be used. The identifier of this vulnerability is VDB-269160. NOTE: The vendor was contacted early about this disclosure but did not respond in any way. | [] | 8.7 | 8.8 | null | null | null | |
CVE-2018-1002207 | mholt/archiver golang package before e4ef56d48eb029648b0e895bb0b6a393ef0829c3 is vulnerable to directory traversal, allowing attackers to write to arbitrary files via a ../ (dot dot slash) in an archive entry that is mishandled during extraction. This vulnerability is also known as 'Zip-Slip'. | [
"cpe:2.3:a:archiver_project:archiver:*:*:*:*:*:*:*:*"
] | null | null | 5.5 | 4.3 | null | |
CVE-2018-15484 | An issue was discovered on KONE Group Controller (KGC) devices before 4.6.5. Unauthenticated Remote Code Execution is possible through the open HTTP interface by modifying autoexec.bat, aka KONE-01. | [
"cpe:2.3:o:kone:group_controller_firmware:*:*:*:*:*:*:*:*",
"cpe:2.3:h:kone:group_controller:-:*:*:*:*:*:*:*"
] | null | null | 9.8 | 10 | null |
This dataset, CIRCL/vulnerability-scores, comprises over 600,000 real-world vulnerabilities used to train and evaluate VLAI, a transformer-based model designed to predict software vulnerability severity levels directly from text descriptions, enabling faster and more consistent triage.
The dataset is presented in the paper VLAI: A RoBERTa-Based Model for Automated Vulnerability Severity Classification.
Project page: https://vulnerability.circl.lu Associated code: https://github.com/vulnerability-lookup/ML-Gateway
Extracted from the database of Vulnerability-Lookup.
Dumps of the data are available here.
import json
from datasets import load_dataset
dataset = load_dataset("CIRCL/vulnerability-scores")
vulnerabilities = ["CVE-2012-2339", "RHSA-2023:5964", "GHSA-7chm-34j8-4f22", "PYSEC-2024-225"]
filtered_entries = dataset.filter(lambda elem: elem["id"] in vulnerabilities)
for entry in filtered_entries["train"]:
print(json.dumps(entry, indent=4))